Understanding Threat Detection, Suricata & Network Intrusion Detection: A Deep Dive
Modern networks face an unprecedented volume of threats—from sophisticated malware to zero-day exploits and insider attacks. Threat detection enables organizations to monitor, analyze, and respond to malicious or anomalous behavior in real-time. This guide dives deeply into threat detection concepts, Suricata as a leading IDS/IPS engine, Network Intrusion Detection Systems (NIDS), and NEOX PacketOwl’s role in packet capture, monitoring, and forensic investigation. Designed for engineers and SOC analysts, this resource goes beyond high-level overviews to provide technical insights, deployment strategies, and advanced operational guidance.
What is Threat Detection? — Technical Perspective
Signature-Based Detection
- Detects threats using predefined patterns such as malware signatures, exploit sequences, or known malicious IPs.
- Advantages: Fast detection for known attacks.
- Limitations: Cannot detect novel or polymorphic threats.
Anomaly-Based Detection
- Establishes baseline behaviors for network traffic, flow characteristics, and protocol usage.
- Flags deviations such as unusual DNS query patterns, unexpected TLS cipher use, or irregular packet sizes.
- Often combined with machine learning models to improve detection accuracy over time.
Protocol & Deep Packet Inspection (DPI)
- Examines both headers and payloads across layers 2–7.
- Detects: Suspicious HTTP requests, SMB lateral movement, FTP malware transfers, or SSH tunneling anomalies.
- Supports extracting and storing files from traffic for further analysis in sandboxes.
Encrypted Traffic Analysis
- Most network traffic is encrypted (HTTPS, TLS, QUIC).
- Detection relies on TLS handshake metadata, JA3/JA3S fingerprints, certificate anomalies, and traffic flow characteristics.
- Advanced techniques include statistical flow analysis, anomaly detection, and optional SSL decryption where policies allow.
Real-Time Alerting & Forensics
- Alerts are generated in milliseconds when anomalies or matches occur.
- Packet capture, session logs, and metadata are retained for detailed forensic reconstruction.
Mastering Threat Detection with Suricata & NIDS requires a deep understanding of these core principles. This foundation is critical for effectively leveraging tools like Suricata to move from simple alerting to true threat hunting and network security monitoring. The subsequent sections will provide a technical deep dive into implementing these methodologies for robust Threat Detection with Suricata & NIDS.

Diagram 1 : Flow of Thread Detection
Deep Dive: Suricata IDS/IPS Engine
Suricata is a multi-threaded, high-performance IDS/IPS/NSM engine that supports signature and anomaly-based detection, protocol parsing, file extraction, and packet capture.
Operational Modes
- IDS (Intrusion Detection System): Monitors mirrored traffic; generates alerts.
- IPS (Intrusion Prevention System): Inline mode; drops or blocks malicious packets.
- NSM (Network Security Monitoring): Logs flows, protocol metadata, alerts; supports threat hunting.
- Full/Conditional Packet Capture: Captures full packets or only triggered sessions for storage.
Technical Features
- Multi-threaded packet processing: Utilizes CPU cores efficiently for high throughput.
- Signature Engine: Supports Snort v2 rules, custom Lua scripts, and ET Open/Pro rulesets.
- Protocol Parsing: Handles HTTP, DNS, SMB, FTP, TLS/SSL, SSH, RTP, SIP, and more.
- File Extraction: Extract files from traffic (attachments, binaries) for sandbox analysis.
- Logging Formats: EVE JSON for easy integration with SIEM and analytics tools.
- High-Performance I/O: Supports AF_PACKET, PF_RING, DPDK for 10/40/100 Gbps networks.
Advanced Use Cases
- Enterprise Monitoring: Detect lateral movement, data exfiltration, malware C2 traffic.
- Cloud Deployments: Suricata containerized in Kubernetes/VMs for east-west traffic inspection.
- Financial Networks: Ultra-low latency detection in trading environments.
- Service Providers: Managed NDR or IDS services for multiple clients.
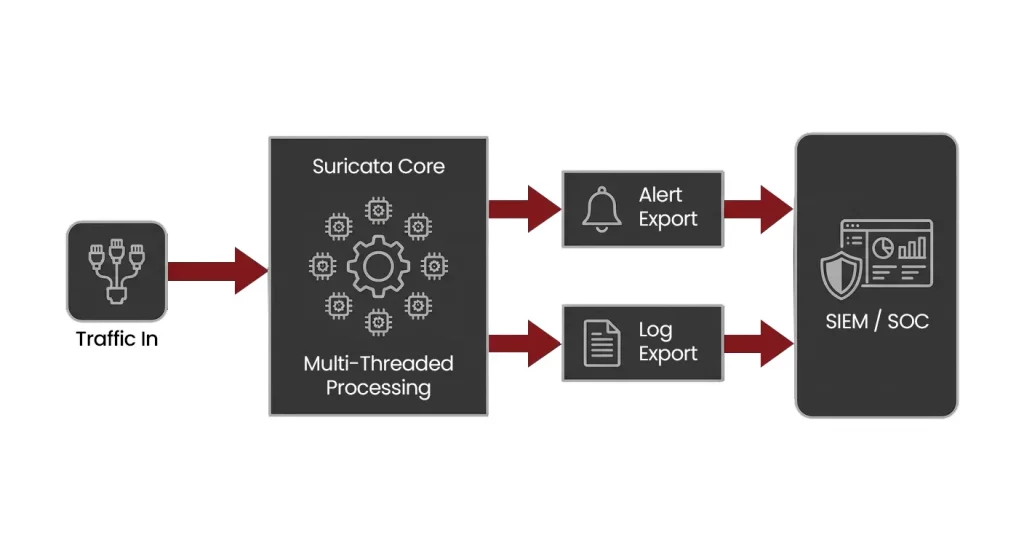
Diagram 2 : Suricata Architecture
Network Intrusion Detection Systems (NIDS) — Technical Overview
A NIDS monitors traffic at network choke points and applies deep inspection to detect malicious behavior.
Key Components
- Traffic Mirroring: TAPs or SPAN ports replicate traffic.
- Deep Packet Analysis: IDS engines analyze all layers and protocols.
- Alerting & Logging: Detailed metadata (source/destination, timestamp, rule matched).
- Packet Capture & Forensics: Stores full PCAPs or triggered session captures.
- Rule Management: Customization and tuning reduce false positives.
Benefits for Technical Teams
- Full network visibility (including lateral movement).
- Real-time detection with minimal false positives.
- Forensic reconstruction using captured packets.
- Threat-hunting capability using historical traffic.
- Regulatory compliance (PCI DSS, GDPR).
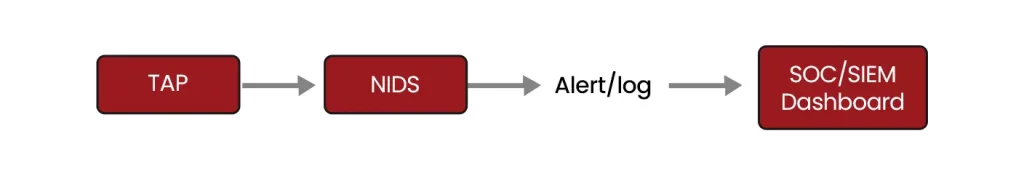
Diagram 3 : NIDS Architecture
NEOX PacketOwl — High-Performance Packet Capture & Threat Detection Support
PacketOwl complements IDS/IPS solutions by providing reliable, high-speed packet capture.
Architecture & Performance
- Line-rate capture at 10/40/100 Gbps with zero packet loss.
- FPGA acceleration for optimized throughput.
- High-capacity NVMe/SSD storage for long-term retention.
Integration with Suricata
- PacketOwl feeds mirrored traffic to Suricata for real-time threat detection.
- Event-triggered PCAP storage ensures all suspicious sessions are retained.
- Export logs and packet data to SIEM/SOC for unified visibility.
Use Cases
- SOC/Enterprise: East-West & North-South monitoring with forensic capture.
- Financial Networks: Ultra-low latency capture and retention for compliance.
- Service Providers: NDR/IDS as a service.
- Cloud Deployments: Virtual PacketOwl instances for traffic capture in VMs/containers.

Diagram 4 : PacketOwl
Advanced Concepts & Best Practices
Rule Management
- Suricata-Update for ET Open/Pro rulesets.
- Custom rules for critical assets, proprietary protocols, or internal applications.
Performance Optimization
- AF_PACKET, PF_RING, DPDK for high-throughput environments.
- Proper tuning of threads, ring buffers, and NIC offloads.
Data Retention & Forensics
- Event-triggered vs continuous capture.
- Archive PCAPs for historical threat hunting.
SOC Integration
- Export alerts and metadata in EVE JSON.
- Visualize in Kibana, Splunk, or Grafana dashboards.
- Conduct forensic analysis and timeline reconstruction.
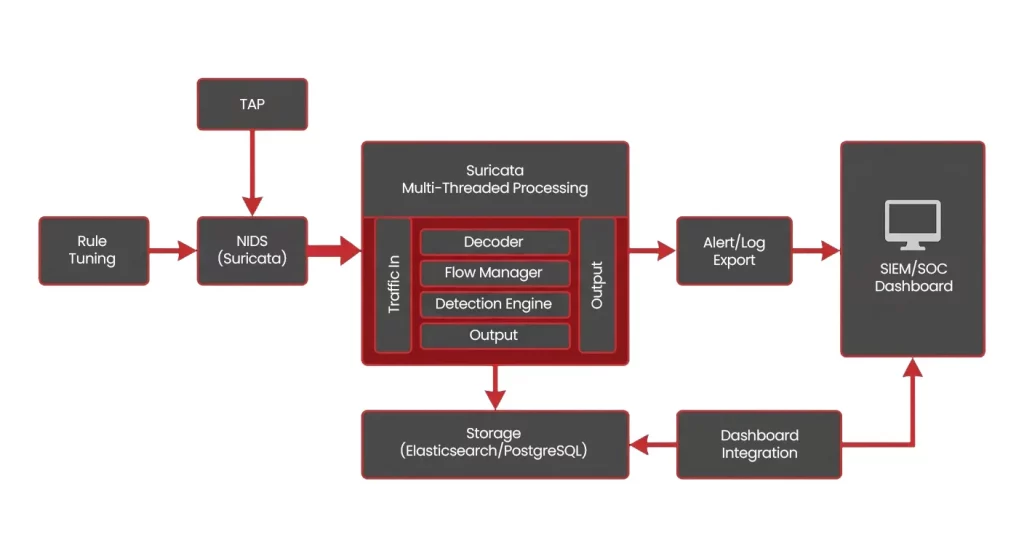
Diagram 5 : Advance Concepts Architecture
FAQs
Can Suricata run IDS and IPS simultaneously?
Typically, one mode at a time; hybrid architectures use passive IDS plus inline IPS.
How does PacketOwl ensure zero packet loss?
Hardware acceleration, high-speed NICs, and optimized I/O paths allow line-rate capture.
Can PacketOwl integrate with TAPs and SPAN ports?
Yes, for clean and unaltered traffic visibility.
What file formats are supported?
PCAP and PCAP-NG, compatible with Wireshark, Zeek, and forensic tools.
How long can traffic be retained?
Depends on model and storage; tiered storage allows long-term retention.

